Jwt Rs256 Generate Key Pair
- Generate Rs256 Key
- Rs256 Generate Key
- Generate Jwt Online
- C# Generate Jwt
- Jwt Rs256 Generate Key Pair 2017
All you wanted to know about JSON Web Tokens but were afraid to ask.
What is JSON Web Token?
JSON Web Token (JWT) is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed. JWTs can be signed using a secret (with HMAC algorithm) or a public/private key pair using RSA.
Let’s explain some concepts of this definition further.
The key to this question is using JWT and Bouncy castle libraries for encoding the token and signing it respectively. JWT for encoding and decoding JWT tokens; Bouncy Castle supports encryption and decryption, especially RS256 get it here; First, you need to transform the private key to the form of RSA parameters. Nov 06, 2019 How to generate JWT RS256 key. GitHub Gist: instantly share code, notes, and snippets. Generate New Keys Async. RSA Encryption Test. Text to encrypt: Encrypt / Decrypt.
- Compact: Because of its size, it can be sent through an URL, POST parameter, or inside an HTTP header. Additionally, due to its size its transmission is fast.
- Self-contained: The payload contains all the required information about the user, to avoid querying the database more than once.
When should you use JSON Web Tokens?
These are some scenarios where JSON Web Tokens are useful:
- Authentication: This is the typical scenario for using JWT, once the user is logged in, each subsequent request will include the JWT, allowing the user to access routes, services, and resources that are permitted with that token. Single Sign On is a feature that widely uses JWT nowadays, because of its small overhead and its ability to be easily used among systems of different domains.
- Information Exchange: JWTs are a good way of securely transmitting information between parties, because as they can be signed, for example using a public/private key pair, you can be sure that the sender is who they say they are. Additionally, as the signature is calculated using the header and the payload, you can also verify that the content hasn’t changed.
Which is the JSON Web Token structure?
JWTs consist of three parts separated by dots (.), which are:
- Header
- Payload
- Signature
Therefore, a JWT typically looks like the following.
xxxxx.yyyyy.zzzzz
Let’s break down the different parts.
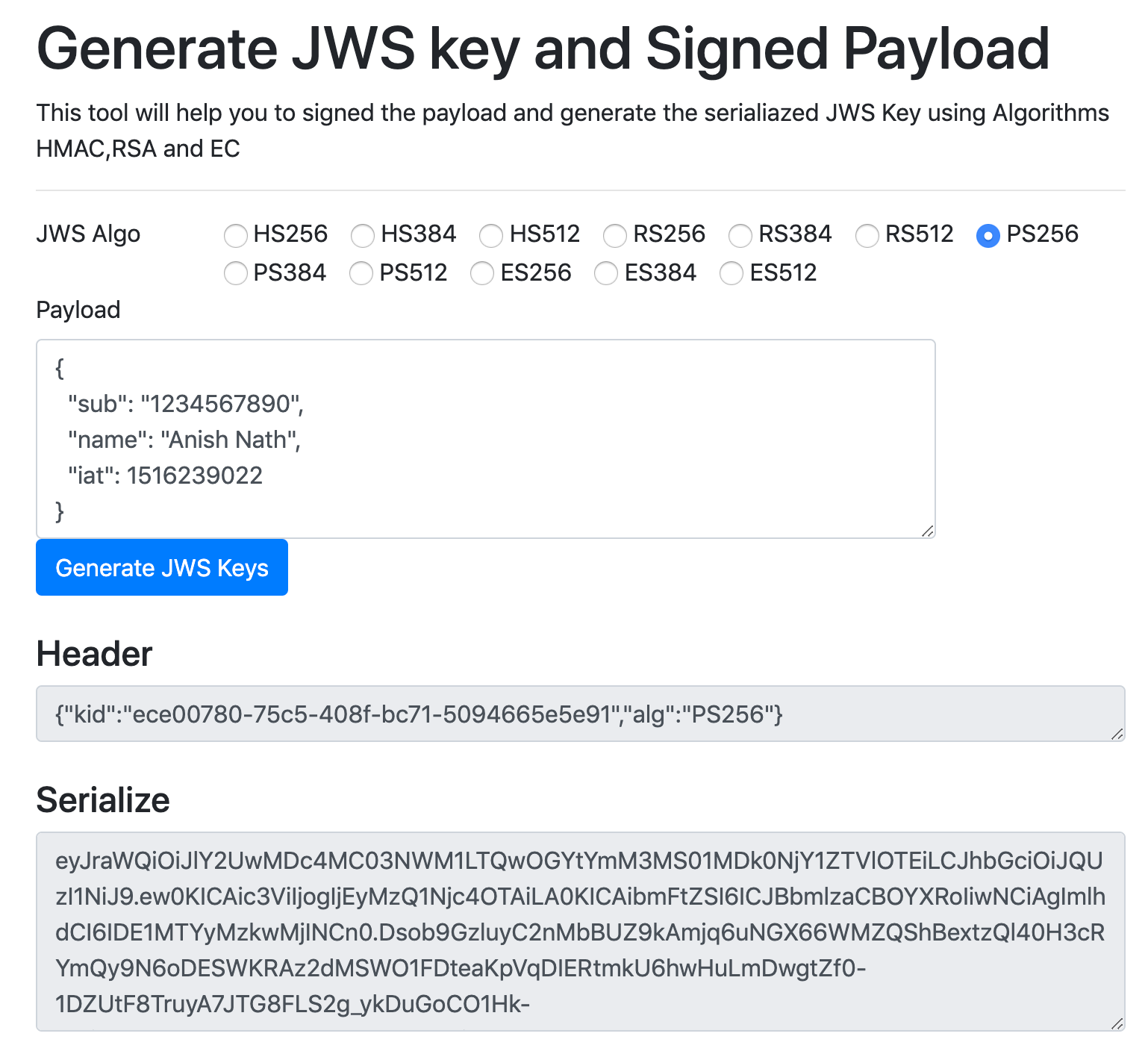
Header
The header typically consists of two parts: the type of the token, which is JWT, and the hashing algorithm such as HMAC SHA256 or RSA.
For example:
Then, this JSON is Base64Url encoded to form the first part of the JWT.
Payload
The second part of the token is the payload, which contains the claims. Claims are statements about an entity (typically, the user) and additional metadata. There are three types of claims: reserved, public, and private claims.
- Reserved claims: These are a set of predefined claims, which are not mandatory but recommended, thought to provide a set of useful, interoperable claims. Some of them are: iss (issuer), exp (expiration time), sub (subject), aud (audience), among others.
Notice that the claim names are only three characters long as JWT is meant to be compact.
- Public claims: These can be defined at will by those using JWTs. But to avoid collisions they should be defined in the IANA JSON Web Token Registry or be defined as a URI that contains a collision resistant namespace.
- Private claims: These are the custom claims created to share information between parties that agree on using them.
An example of payload could be:
The payload is then Base64Url encoded to form the second part of the JWT.
Signature
To create the signature part you have to take the encoded header, the encoded payload, a secret, the algorithm specified in the header, and sign that.
For example if you want to use the HMAC SHA256 algorithm, the signature will be created in the following way.
The signature is used to verify that the sender of the JWT is who it says it is and to ensure that the message was’t changed in the way.
Putting all together
The output is three Base64 strings separated by dots that can be easily passed in HTML and HTTP environments, while being more compact compared to XML-based standards such as SAML.
The following shows a JWT that has the previous header and payload encoded and it is signed with a secret.
You can browse to jwt.io where you can play with a JWT and put these concepts in practice. /team-foundation-server-license-key-generator.html. jwt.io allows you to decode, verify and generate JWT.
How JSON Web Tokens work?
In authentication, when the user successfully logs in using their credentials, a JSON Web Token will be returned. Since tokens are credentials, great care must be taken to prevent security issues. In general, you should not keep tokens longer than required.
You also should not store sensitive session data in browser storage due to lack of security.
Whenever the user wants to access a protected route, it should send the JWT, typically in the Authorization header using the Bearer schema. Therefore the content of the header should look like the following.
Authorization: Bearer <token>
This is a stateless authentication mechanism as the user state is never saved in the server memory. The server’s protected routes will check for a valid JWT in the Authorization header, and if there is, the user will be allowed. As JWTs are self-contained, all the necessary information is there, reducing the need of going back and forward to the database.
This allows to fully rely on data APIs that are stateless and even make requests to downstream services. It doesn’t matter which domains are serving your APIs, as Cross-Origin Resource Sharing (CORS) won’t be an issue as it doesn’t use cookies.
Why should you use JSON Web Tokens?
Let’s talk about the benefits of JSON Web Tokens (JWT) comparing it to Simple Web Tokens (SWT) and Security Assertion Markup Language Tokens (SAML).
As JSON is less verbose than XML, when it is encoded its size is also smaller; making JWT more compact than SAML. This makes JWT a good choice to be passed in HTML and HTTP environments.
Security-wise, SWT can only be symmetric signed by a shared secret using the HMAC algorithm. While JWT and SAML tokens can also use a public/private key pair in the form of a X.509 certificate to sign them. However, signing XML with XML Digital Signature without introducing obscure security holes is very difficult compared to the simplicity of signing JSON.
JSON parsers are common in most programming languages, because they map directly to objects, conversely XML doesn’t have a natural document-to-object mapping. This makes it easier to work with JWT than SAML assertions.
Regarding usage, JWT is used at an Internet scale. This highlights the ease of client side processing of JWTs on multiple platforms, especially, mobile.
How we use JSON Web Tokens in Auth0?
In Auth0, we issue JWTs as a result of the authentication process. When the user logs in using Auth0, a JWT is created, signed, and sent to the user. Auth0 supports signing JWT with both HMAC and RSA algorithms. This token will be then used to authenticate and authorize with APIs which will grant access to their protected routes and resources.
We also use JWTs to perform authentication and authorization in Auth0’s API v2, replacing the traditional usage of regular opaque API keys. Regarding authorization, JSON Web Tokens allow granular security, that is the ability to specify a particular set of permissions in the token, which improves debuggability.
2018-06-11T14:15:42Z
JSON Web Tokens offer a simple and powerful way to generate tokens for APIs. These tokens carry a payload that is cryptographically signed. While the payload itself is not encrypted, the signature protects it again tampering. In their most common format, a 'secret key' is used in the generation and verification of the signature. In this article I'm going to show you a less known mechanism to generate JWTs that have signatures that can be verified without having access to the secret key.
Quick Introduction to JSON Web Tokens (JWTs)
In case you are not familiar with JWTs, let me first show you how to work with them using Python with the pyjwt package. Create a virtual environment, and install pyjwt in it:
Now let's say you want to create a token that gives a user with id 123 access to your application. After you verify that the user has provided the correct username and password, you can generate a token for the user:
The jwt.encode() function has three arguments of which the most important is the first, containing the token payload. This is the information that you want stored in the token. You can use anything that can be serialized to a JSON dictionary as a payload. The payload is where you record any information that identifies the user. In the simplest case this is just the user id like in the example above, but you can include other user information such as a username, user roles, permissions, etc. Here is a more complex token:
As you can see, the more data you write in the payload, the longer the token is, because all that data is physically stored in the token. By looking at the resulting JWTs you may think that the data that you put in the tokens is encrypted, but this is actually incorrect. You should never write sensitive data in a JWT, because there is no encryption. This seemingly random sequence of characters that you see in these tokens is just generated with a simple base64 encoding.
In addition to user information, the payload of a JWT can include a few fields that apply to the token itself, and have a predefined meaning. The most useful of these is the exp field, which defines an expiration time for the token. The following example gives the token a validity period of 5 minutes (300 seconds):
Other predefined fields that can be included in the JWT are nbf (not before), which defines a point in time in the future at which the token becomes valid, iss (issuer), aud (audience) and iat (issued at). Consult the JWT specification if you want to learn more about these.
The second argument to jwt.encode() is the secret key. This is a string that is used in the algorithm that generates the cryptographic signature for the token. The idea is that this key must be known only to the application, because anyone who is in possession of this key can generate new tokens with valid signatures. In a Flask or Django application, you can pass the configured SECRET_KEY for this argument.
The last argument in the jwt.encode() call is the signing algorithm. Most applications use the HS256 algorithm, which is short for HMAC-SHA256. The signing algorithm is what protects the payload of the JWT against tampering.
The value returned by jwt.encode() is a byte sequence with the token. You can see in all the above examples that I decoded the token into a UTF-8 string, because a string is easier to handle.
Once your application generates a token it must return it to the user, and from then on, the user can authenticate by passing the token back to the server, which prevents the user from having to constantly send stronger credentials such as username and password. Using JWTs for authentication is considered more secure than usernames and passwords, because you can set an appropriate expiration time, and in that way limit the damage that can be caused in the case of a leak.
When the application receives a JWT from the user it needs to make sure that it is a legitimate token that was generated by the application itself, which requires generating a new signature for the payload and making sure it matches the signature included with the token. Using the first of the example tokens above, this is how the verification step is done with pyjwt:
The jwt.decode() call also takes three arguments: the JWT token, the signing key, and the accepted signature algorithms. Note how in this call a list of algorithms is provided, since the application may want to accept tokens generated with more than one signing algorithm. Note that while the algorithms argument is currently optional in pyjwt, there are potential vulnerabilities that can occur if you don't pass the list of algorithms explicitly. If you have applications that call jwt.decode() and don't pass this argument, I strongly advise you to add this argument.
The return value of the jwt.decode() call is the payload that is stored in the token as a dictionary ready to be used. If this function returns, it means that the token was determined to be valid, so the information in the payload can be trusted as legitimate.
Let's try to decode the token from above that had an associated expiration time. I have generated that token more than five minutes ago, so even though it is a valid token, it is now rejected because it has expired:
It is also interesting to see what happens if I take one of the tokens above, make a change to any of the characters in the string and then try to decode it:
So as you see, if jwt.decode() returns back a dictionary, you can be sure that the data in that dictionary is legitimate and can be trusted (at least as much as you are sure your secret key is really secret).
Using Public-Key Signatures with JWTs

A disadvantage of the popular HS256 signing algorithm is that the secret key needs to be accessible both when generating and validating tokens. For a monolithic application this isn't so much of a problem, but if you have a distributed system built out of multiple services running independently of each other, you basically have to choose between two really bad options:
- You can opt to have a dedicated service for token generation and verification. Any services that receive a token from a client need to make a call into the authentication service to have the token verified. For busy systems this creates a performance bottleneck on the authentication service.
- You can configure the secret key into all the services that receive tokens from clients, so that they can verify the tokens without having to make a call to the authentication service. But having the secret key in multiple locations increases the risk of it being compromised, and once it is compromised the attacker can generate valid tokens and impersonate any user in the system.
So for these types of applications, it would be better to have the signing key safely stored in the authentication service, and only used to generate keys, while all other services can verify those tokens without actually having access to the key. And this can actually be accomplished with public-key cryptography.
Public-key cryptography is based on encryption keys that have two components: a public key and a private key. As it name imples, the public key component can be shared freely. There are two workflows that can be accomplished with public-key cryptography:
- Message encryption: If I want to send an encrypted message to someone, I can use that person's public key to encrypt it. The encrypted message can only be decrypted with the person's private key.
- Message signing: If I want to sign a message to certify that it came from me, I can generate a signature with my own private key. Anybody interested in verifying the message can use my public key to confirm that the signature is valid.
There are signing algorithms for JWTs that implement the second scenario above. Tokens are signed with the server's private key, and then they can be verified by anyone using the server's public key, which is freely available to anyone who wants to have it. For the examples that follow I'm going to use the RS256 signing algorithm, which is short for RSA-SHA256.
The pyjwt package does not directly implement the cryptographic signing functions for the more advanced public-key signing algorithms, and instead depends on the cryptography package to provide those. So to use public-key signatures, this package needs to be installed:
The next step is to generate a public/private key set (usually called a 'key pair') for the application to use. There are a few different ways to generate RSA keys, but one that I like is to use the ssh-keygen tool from openssh:
The -t option to the ssh-keygen command defines that I'm requesting an RSA key pair, and the -b option specifies a key size of 4096 bits, which is considered a very secure key length. When you run the command you will be prompted to provide a filename for the key pair, and for this I used jwt-key without any path, so that the key is written to the current directory. Then you will be prompted to enter a passphrase to protect the key, which needs to be left empty.
When the command completes, you are left with two files in the current directory, jwt-key and jwt-key.pub. The former is the private key, which will be used to generate token signature, so you should protect this very well. In particular, you should not commit your private key to your source control, and instead should install on your server directly (you should keep a well protected backup copy of it, in case you ever need to rebuild your server). The .pub file will be used to verify tokens. Since this file has no sensitive information, you can freely add a copy of it on any project that needs to verify tokens.
The process to generate tokens with this key pair is fairly similar to what I showed you earlier. Visual certexam suite 3.4 2 serial key generator. Let's first make a new token:
The main difference with the previous tokens is that I'm passing the RSA private key as the secret key argument. The value of this key is the entire contents of the jwt-key file. The other difference is that the algorithm requested is RS256 instead of HS256. The resulting token is longer, but otherwise similar to those I generated previously. Like the previous tokens, the payload is not encrypted, so also for these tokens you should never put sensitive information in the payload.
Now that I have the token, I can show you how it can be verified using the public key. If you are trying this with me, exit your Python session and start a new one, to make sure there is no trace of the private key in the Python context. Here is how you can verify the token above:
Generate Rs256 Key
This example looks nearly identical to the previous ones, but the important fact is that we are ensuring this token is valid without access to any sensitive information. The server's public key presents no risk, so it can be freely shared with the world. And in fact, anybody would be able to verify the tokens that your application generates with this key. To prove this point, let me share with you my public key:
You can now take this public key and validate the token that I generated, and letting you validate the tokens does not introduce any security risks for me. I'm still the only person in the world that can generate new tokens.
Rs256 Generate Key
Conclusion
Generate Jwt Online
I hope those of you who were using JWTs with the popular HS256 algorithm are now ready to introduce RS256 or any of the other public-key signature options available.
Let me know if you have any questions in the comment area below!
C# Generate Jwt
Hello, and thank you for visiting my blog! If you enjoyed this article, please consider supporting my work on this blog on Patreon!
41 comments
#1Ars said 2018-06-11T19:42:22Z
#2Miguel Grinberg said 2018-06-11T22:34:20Z
#3JM said 2018-07-06T00:47:09Z
#4Miguel Grinberg said 2018-07-06T05:37:07Z
#5Abdul Wahab van Reenen said 2018-07-30T10:21:35Z
#6Miguel Grinberg said 2018-07-30T21:02:35Z
#7SG said 2018-08-07T00:35:35Z
#8Miguel Grinberg said 2018-08-07T21:18:10Z
#9Mitch said 2018-08-19T22:08:06Z
#10stm said 2018-09-07T07:24:16Z
#11Miguel Grinberg said 2018-09-13T20:51:35Z
#12grex_e said 2018-10-17T23:52:59Z
#13Miguel Grinberg said 2018-10-18T14:19:33Z
#14grex_e said 2018-10-20T23:40:32Z
#15Vladyslav said 2018-11-01T09:58:18Z
#16yoni said 2018-11-10T00:18:03Z
#17Akshay said 2018-12-11T21:12:23Z
#18Miguel Grinberg said 2018-12-12T15:21:26Z
#19simi403 said 2018-12-19T18:24:52Z
#20Miguel Grinberg said 2018-12-19T22:19:59Z
#21Kim said 2019-02-24T00:28:17Z
#22Miguel Grinberg said 2019-02-24T19:47:17Z
#23Saqib said 2019-04-12T10:10:24Z
#24Miguel Grinberg said 2019-04-12T18:34:58Z
#25Andy said 2019-08-17T13:19:30Z